Wireless Intrusion Prevention System (WIPS) Deployment Architectures – Overlay, Integrated & Hybrid
So, as mentioned above, a wireless intrusion prevention system continuously scans for various wireless threats over the air and reports the same, when found. Some of them are automatically configured to take action like initiating a reverse DOS attack on the offending client/AP so that the misbehaving client/AP cannot connect to the network.
As you might be knowing, a wireless network consists of a centralized wireless controller, access points, and some servers for specialty applications. All the laptops/ wi-fi enabled devices connect to the access point to communicate with the wireless network over the air (wireless medium). Now, some organizations deploy a wireless intrusion prevention system to secure their wireless networks, as the wireless network signals are available outside the campus as well. WIPS solutions can be deployed in different ways. We discuss some of the popular WIPS architectures, and their merits and demerits, in this article.
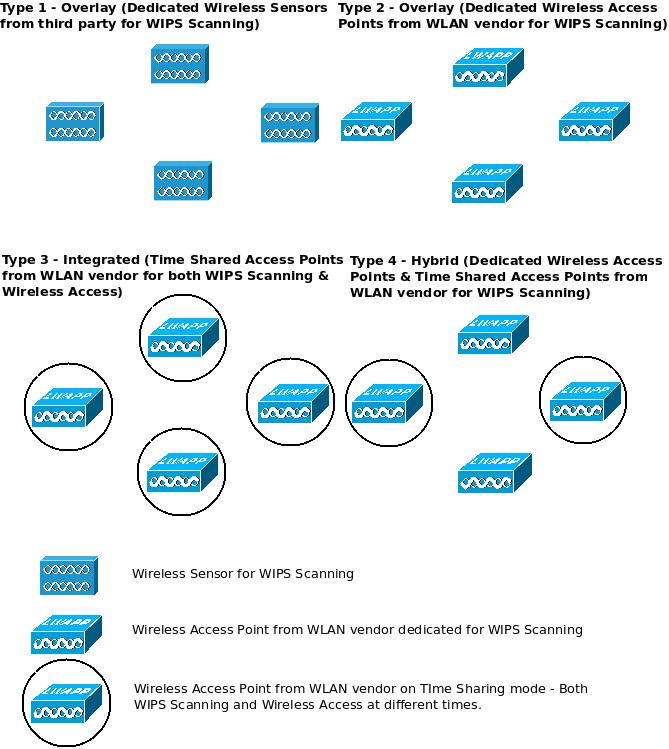 The Wireless Intrusion Prevention Systems can be deployed in many ways. We will discuss four popular ones in this article.
The Wireless Intrusion Prevention Systems can be deployed in many ways. We will discuss four popular ones in this article.
Type 1 – Overlay (Dedicated Wireless Sensors from third party for WIPS Scanning):
One popular WIPS deployment architecture is using dedicated wireless sensors (which are like access points, but hardened and purpose built for wireless security scanning only) and a centralized server that does threat analysis. Generally these devices are provided by a specialized manufacturer who is different from the Wireless LAN solution vendor.
The first obvious advantage is that they are dedicated to the task of wireless scanning. So, they can scan all the channels quickly for possible intrusions. Some of them claim that they offer comprehensive regulatory compliance and forensics analysis, though that may be vendor dependent. Some of them can store security event data in the sensors itself, for a limited period of time, and some of them can locally analyze all the packets and send only certain selected events that match threat pattern, to the central server for further processing. This might make distributed deployments of such sensors (over the WAN), easier.
This type of deployment is good for companies having high volume wireless data transfer as the security data is captured and analyzed separately. The cost of such a solution though, might be on the higher side, when compared to others. These dedicated sensors are security hardened and do not divulge information like vendor name, firmware version etc, on casual probing by hackers. These sensors cannot work as normal access points for wireless traffic forwarding. They may not be able to give location information of misbehaving clients/AP’s.
Encrypted wireless traffic cannot be analyzed by these sensors. So, insider attacks and few application layer attacks are hard to detect. The best a sensor can do to stop an attack is to counter attack through methods like Reverse DOS. But there is a possibility that the misbehaving client can disassociate from the current access point and try attacking the next one.
Type 2 – Overlay (Dedicated Access Points from WLAN vendor for WIPS Scanning):
In this architecture, certain wireless access points from the Wireless LAN vendor are dedicated for WIPS Scanning and monitoring instead of using third party wireless sensors. The obvious advantages would be the common administration interface, bulk purchase (along with wireless access points) and single vendor maintenance.
The traffic from these access points, more often than not, is sent to the centralized controller/ server for security analysis. This increases the strain on the performance of the wireless controller. There is a higher chance that a general purpose access point can be compromised by a hacker, than a specialized wireless sensor. Access Points are generally made to operate in legally allowed channels of a particular country. Hence, if a hacker is using other channels, they might go undetected.
Since these are normal access points, they can be used for traffic forwarding and other wireless LAN functions if need arises (like an event where too many unexpected wireless users accumulate). Location identification services to detect the misbehaving client/AP can be implemented with this solution. Even encrypted traffic can be scanned and misbehaving clients can be cut off from connecting to any of the access points in the network.
Type 3 – Integrated (Time Shared Access Points from WLAN vendor for Wireless Access as well as WIPS Scanning):
Some vendors offer access points that can give wireless access as well as scan for wireless threats, simultaneously on a time-shared basis(The access points forward wireless data traffic for some time and scans the airwaves for security threats at other times). So, as you might have guessed, this solution uses the minimum number of access points (both combined) and is cost effective. This could be implemented in companies with a tight budget and less demanding wireless usage. But for this architecture, the con’s outweigh the pro’s!
The access points in this architecture cannot perform both scanning and traffic forwarding at the same time (simultaneously), and this impacts the performance for both. Especially, when real time applications like voice and video are used over wireless. While the channel in which the access point is forwarding traffic can be scanned for wireless threats, it does not monitor the other channels frequently. An access point in this mode, cannot block an intrusion simultaneously as it is forwarding traffic.
The biggest disadvantage of this architecture is the little time (relatively) spent for WIPS scanning and more often than not, scanning for wireless threats is sacrificed for wireless data traffic forwarding. More over, all the channels are not scanned frequently, resulting in increased chances for wireless attacks. Other than these, all the disadvantages of type-2 architecture apply for this one as well.
Type 4 – Hybrid (Mix of Dedicated Wireless Access Points & Time Shared Access Points from WLAN vendor for WIPS Scanning):
Well, this is actually a compromise between type-2 & type-3 architectures. This one is about deploying dedicated access points for wireless threat mitigation as far as possible, but it also advocates the usage of some access points on a time-shared basis at the same time. For example, dedicated WIPS scanning access points can be used at dense wireless deployment scenarios & strategic regions and shared access points at other less demanding places. The advantages and disadvantages are same as the above two types (type-2, type-3) of architectures.
excITingIP.com
You could keep yourself updated with the various computer networking technologies by subscribing to this blog with your email address in the box mentioned as “Get Email Updates when new Articles are Published”.